In evaluating a phone number’s trustworthiness, the guide emphasizes tracing provenance and context over impression. The approach favors verifiable signals—caller ID history, business records, and independent cross-checks—while wary of pressure tactics and unverifiable claims. It suggests safe, privacy-preserving profiling to confirm identity without exposing sensitive data, and it demands transparency about sources and biases. Yet questions linger: will these checks be enough when motives stay concealed and details blur?
How to Verify a Phone Number’s Source and Intent
To determine a caller’s origin and motive, one should scrutinize the traceable clues embedded in the call’s metadata and the caller’s behavior rather than rely on impression alone. The piece examines verify source signals, confirm intent, and red flags, using tracing tools to assess provenance. It emphasizes protecting info, skeptical inquiry, and disciplined evidence over assumptions.
Scams Indicators: Red Flags to Watch in Real Time
In real-time phone scrutiny, what indicators emerge that distinguish legitimate calls from scams, and how reliably can these signals be interpreted as evidence?
The narrative remains inquisitive, evidentiary, skeptical, noting that phone scams often exploit urgency, pressure, or unverifiable caller verification. Yet ambiguity persists; red flags may mislead. Cautious assessment prioritizes verifiable data over assumptions in any pursuit of freedom.
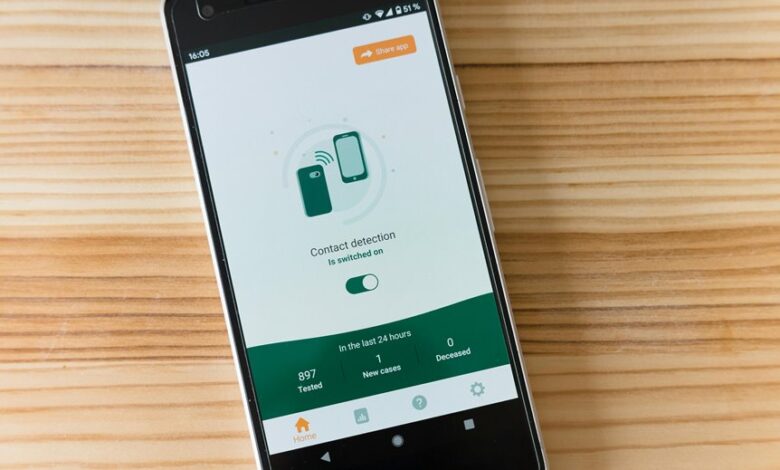
Tools and Methods to Trace Numbers Safely
As concerns about scam indicators from real-time scrutiny persist, the discussion moves to how numbers can be traced safely through available tools and methods that minimize risk while maximizing verifiable results.
Inquiries center on phone verification, caller profiling, emergency safety, data privacy; skepticism remains about data sources, permissions, and potential biases, urging transparent, user-empowered approaches for trustworthy traceability.
Confirming Who’s on the Line and Protecting Your Info
Is it possible to reliably identify who is on the line while safeguarding personal information, or do safeguards compromise transparency? In probing this, the article examines verifiable cues and ethical limits. A skeptical view emerges: verify caller claims, assess trace safety, and compare number source data without exposing sensitive identifiers. The goal remains freedom, not coercive surveillance, with data protection guiding practical transparency.
Conclusion
The guide closes like a locked mailbox: signals await verification, silence betrays nothing, and urgency is a feathered trap. Each number stands as a cipher, its provenance a quiet ledger. The investigator, armed with traceable clues and cross-checks, asks the questions the caller won’t answer. In the end, trust must be earned, not assumed—until data aligns, the line remains a garden of shadows, where caution plants the only reliable fruit.